Fishing for hackers: Analysis of Linux Server Attack
4.7 (654) In stock
4.7 (654) In stock

10 industry-defining security incidents from the last decade

M S Sk

Analysis of Attacks That Install Scanners on Linux SSH Servers

Ethical Hacking using Kali Linux

Query Graph of Scenario: Linux-2 (on the left) and its Detected

Best Ethical Hacking Tools 100 Hacking Tools & Software
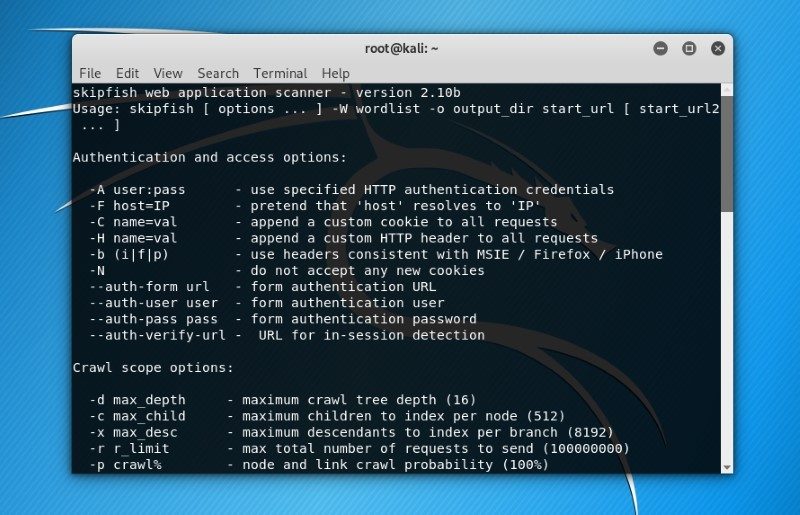
21 Best Kali Linux Tools for Hacking and Penetration Testing
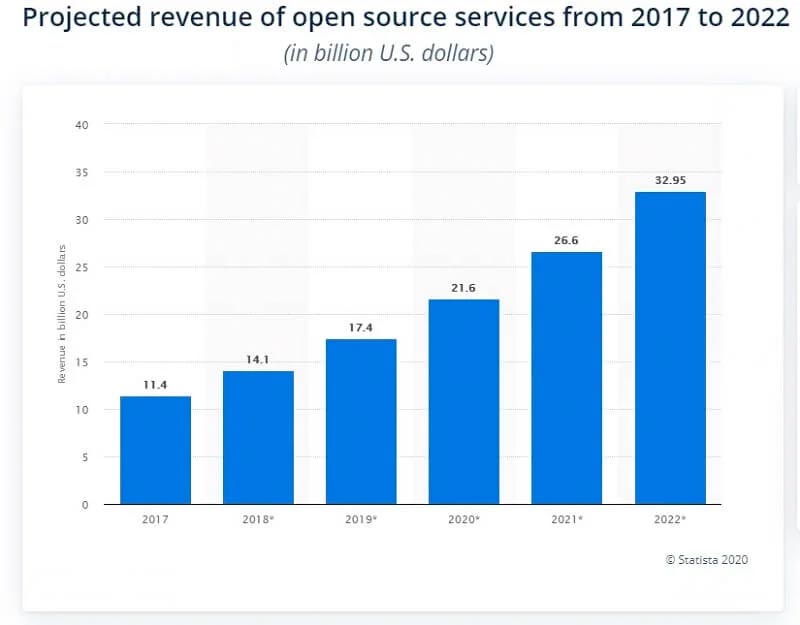
Free and Open Source Software (FOSS) for Cybersecurity Teams

34 Linux Server Security Tips & Checklists for Sysadmins
How to Extract Memory Information to Spot Linux Malware
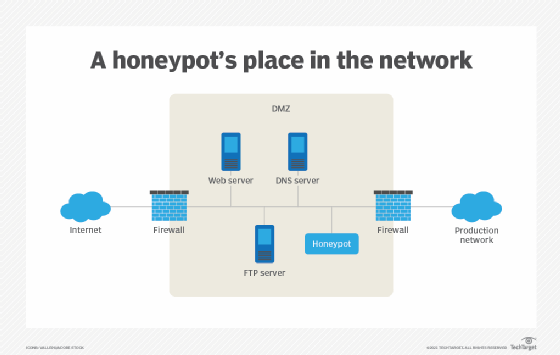
What is a honeypot? How it protects against cyber attacks

Kali Linux 2020.3 Release - Penetration Testing and Ethical

Hackers Use Java to Hide Malware on the Data Center Network